What is ISO27001?
ISO27001 is an international standard that provides a framework for an information security management system (ISMS).
ISO27001 is important for payroll software as it sets out requirements for an effective information security management system, including risk assessment and treatment, security controls and continual improvement.
An ISO27001-compliant information security management system can help payroll companies with HMRC-recognised payroll software to protect their data and systems from threats, and to ensure compliance with relevant laws and regulations. An information security management system is a framework of policies and procedures that includes all legal, physical and technical controls involved in an organisation's information risk management processes.
How does ISO27001 help payroll companies?
ISO27001 is a globally recognised standard, and certification gives payroll companies a competitive advantage over non-certified payroll companies by demonstrating the importance of security within the organisation.
ISO27001 was first published in 2005. It is currently in its second edition (2013). ISO27001 is developed by ISO/IEC. The previous version was known as ISO/IEC 27001:2005.
ISO27001 is a voluntary standard, but many organisations choose to implement it in order to improve their security position and to demonstrate their commitment to security. ISO27001 certification is available from a number of certification bodies. To be ISO27001 certified, an organisation must have its information security management system audited by a certified auditor and must meet all the requirements of the standard.
What standards need to be met to gain ISO27001 certification?
As each company faces different security threats and challenges, there is no generic ‘one size fits all’ standard. Instead, ISO27001 requires proof of security policies and processes that document the steps taken to ensure information security within the company. The following information is mandatory for ISO27001 certification:
- Scope of the information security management system (ISMS).
This document defines the type of operations to be covered by the information security management system. It also sets the boundaries of the ISMS as some of the organisation may be covered by the ISMS, whereas some of the organisation may be excluded from the ISMS. The scope of the document must include the products and/or services that are provided and the geographical location as well as which parts of the organisation the ISMS will be applicable to. It also defines the processes, policies and procedures.
- Information security policy and objectives.
This document is a statement of the company’s goal for information handling. It requires the company to act in a way which complies with its legal obligations. It also defines the company’s goal to meet its ethical obligations as well as continually strive for improvement in the area of information handling and security.
- Risk assessment and risk treatment methodology.
This is the document that sets out how risk to security of information is identified and how the risks will be addressed once identified. Individual risks do not need to be included in this document. This document is about the methodology of identifying, owning and assessing the risks. It should also include a risk severity matrix and the likelihood of the levels of risk occurring.
- Statement of Applicability.
There are over one hundred security controls listed in Annexe A of ISO27001. This document defines which of the security controls will be implemented and provides the reasons why they will be implemented. The organisation seeking certification needs to identify and document which of the controls are applicable to their business and demonstrate how they have been implemented.
- Risk Treatment Plan.
Once the controls have been identified and documented in the Statement of Applicability, this document demonstrates how the identified controls will be implemented and who will be responsible for their implementation. The plan should also defines time frames for implementation and the resources that are required to effect successful implementation.
- Risk assessment and risk treatment report.
This document is a report on a risk assessment, and any risk treatment, performed in line with the risk assessment and risk treatment policy. This document will report on the findings of the risk assessment and the mitigation strategies that have been taken to mitigate risk.
- Definition of security roles and responsibilities. This document outlines the responsibilities of personnel within the business who play a role in the security of information.
- Inventory of assets.
This document sets out the list of assets that are utilised for the storage of data across the organisation. This lists all physical hardware as well as documentation, cloud storage and off-site data recovery solutions.
- Acceptable use of assets.
This is a policy document which sets out to employees, contractors and suppliers the acceptable use of devices and storage listed in the Inventory of assets. This policy should include information of encryption, security of assets, acceptable use inside and outside of the organisation, personal use etc.
- Access control policy.
This document defines who, within the organisation, is granted access to sensitive information.
- Operating procedures for IT management.
This document includes procedures that should be implemented in the event that the Acceptable use of assets policy document is breached or through the incorrect operation of equipment.
- Secure system engineering principles.
This document defines how security will be applied in the development of new solutions or projects which affect the existing infrastructure. The document should also contain the disaster recovery procedures and business continuity plan.
- Supplier security policy.
This document is the policy of security of information from suppliers. Any suppliers who may have been identified in the risk assessment should be focused upon so that data is not exposed to risk through corruption, theft or destruction.
- Incident management procedure.
This document details the procedures that will be followed in the event of an information security incident. Incident ownership should be defined in this document as well as the procedure that will be followed for data gathering; the circumstances around the information security breach; escalation procedures and resolution procedures should be included in the document.
- Business continuity procedures.
The procedure for business continuity in the event of an information security breach are included in this document. The information should contain detail on the roles and responsibilities for actions and timescales to ensure business continuity. This document should also include information on escalation of the security incident to regulatory bodies.
- Legal, regulatory, and contractual requirements.
This document sets out the legal, regulatory and contractual requirements and is a reference document for employees, suppliers and contractors to the organisation.
- Records of training, skills, experience and qualifications.
This document is a reference document to demonstrate that all employees within the organisation that are involved in the security of information have the relevant training and expertise to carry out their responsibilities effectively.
- Monitoring and measurement of results.
This document provides demonstrable evidence of the company’s commitment to, and achievement of, continual improvement. This is an important document when the time comes for re-certification.
- Internal audit programme and results.
A programme of internal audits is an important part of the information security management system. Internal audits measure and report on information security within the organisation and measure compliance with the processes set out in the ISMS documentation.
- Results of the management review.
Senior management should regularly review the ISMS to make sure that it remains effective, and a record should be kept of the results of these reviews in line with the standard.
- Non-conformities and results of corrective actions.
This document includes any non-conformities in the organisation’s processes and operations. It should also include any actions taken to address the non-conformities and how these will be prevented in the future.
- Logging user activities, exceptions and security events.
Effective logging of activity is an important tool for maintaining the security of information. Records of activity, including any security incidents and how they were corrected can be built in to future risk assessment and mitigation planning to prevent future incidences and demonstrate continual improvement for re-certification.
How do I check if a company is ISO27001 certified?

There's no central register of ISO 27001 certificates. To check certification, the easiest way is to request a copy of the supplier’s certificate and identify the certification body that issued the certificate.
The certifying body should be verified as a member of the International Accreditation Forum (‘IAF’), which is a worldwide association of accreditation bodies.Their primary function is to develop a single worldwide programme of conformity assessment.
This reduces risk for businesses and their customers by assuring them that accredited certificates and validation and verification statements may be relied upon. Once this has been verified, a request can be made to the certifying body to confirm the validity of the certification.
In summary, ISO27001 is an important standard for payroll companies. It provides a framework for an effective information security management system. ISO27001-compliant information security management systems help payroll companies to protect data and systems from threats, and to ensure compliance with relevant laws and regulations.
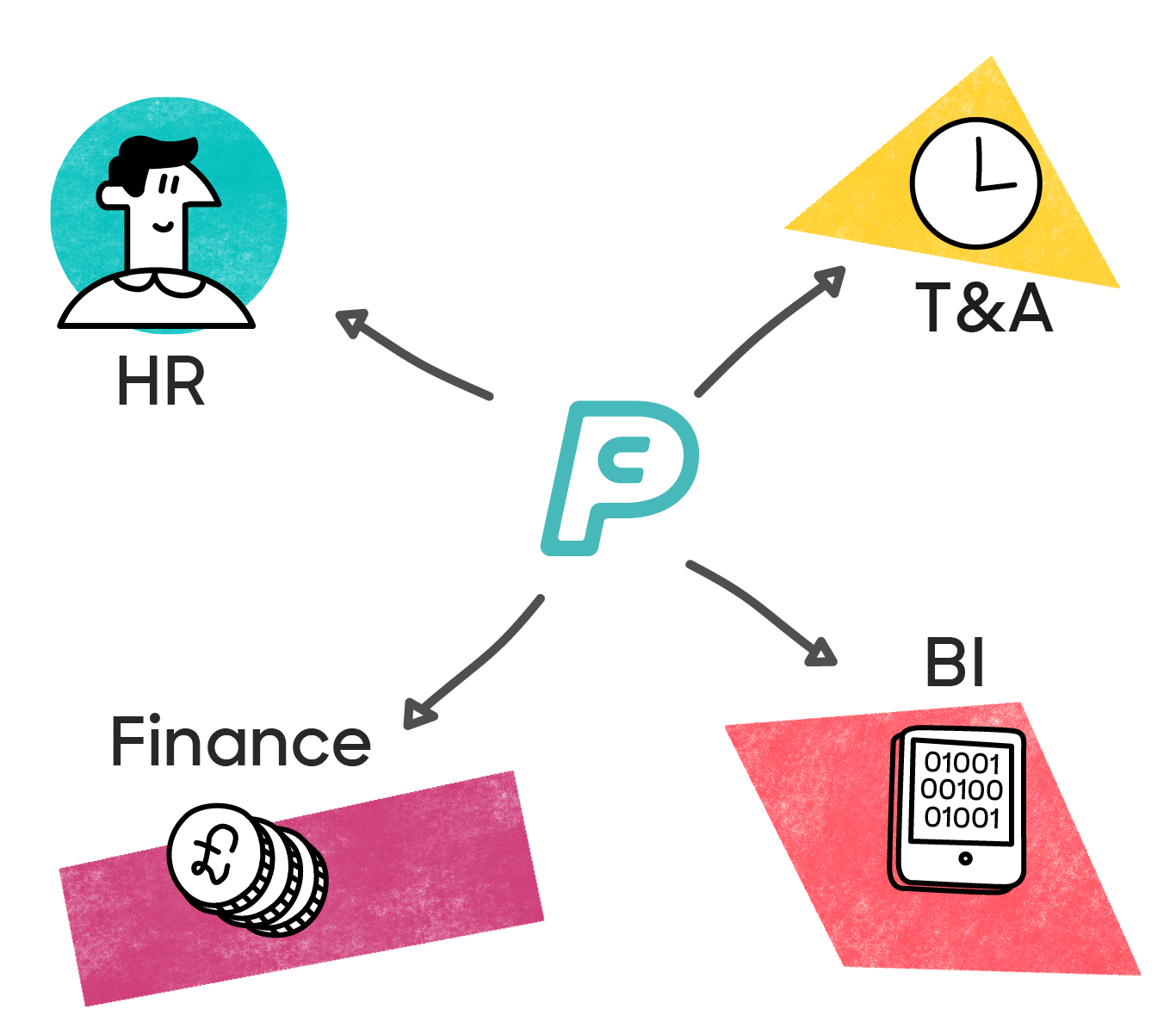
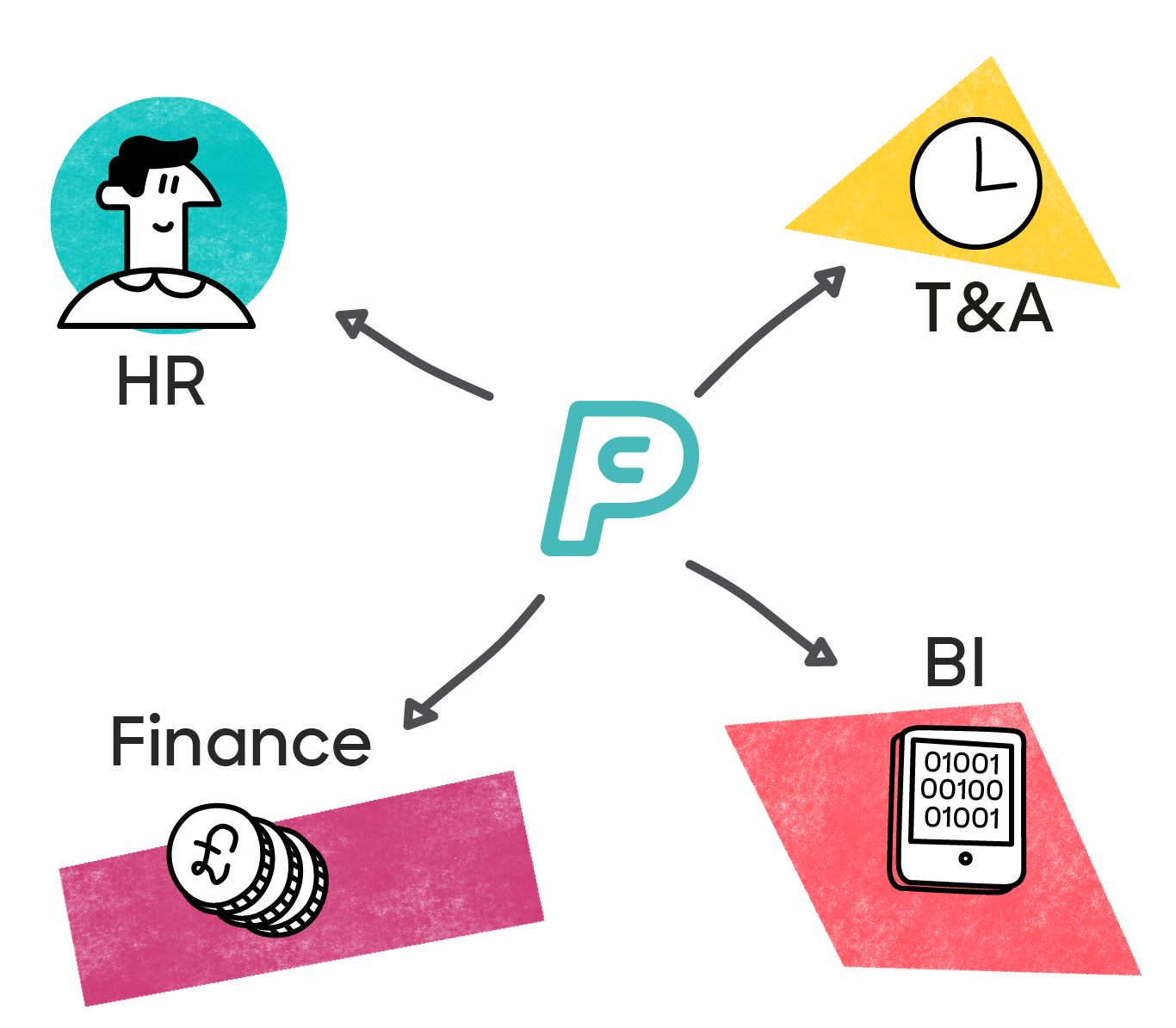
ISO27001 is a voluntary standard. To gain ISO27001 certification, organisations must go through a rigorous process to protect their data as well as demonstrate their commitment to security and continual improvement. PayCaptain is a certified ISO27001 organisation. Click here to see our ISO27001 certificate.
To learn more about how PayCaptain can help your business, contact us for an informal, no obligation chat. We’ll be happy to demo PayCaptain for you.















.png)
